Oracle Vault
Oracle Vault
External Secrets Operator integrates with OCI API to sync secret on the Oracle Vault to secrets held on the Kubernetes cluster.
Authentication
If auth is not specified, the operator uses the instance principal.
For using a specific user credentials, userOCID, tenancyOCID, fingerprint and private key are required. The fingerprint and key file should be supplied in the secret with the rest being provided in the secret store.
See url for what region you you are accessing.

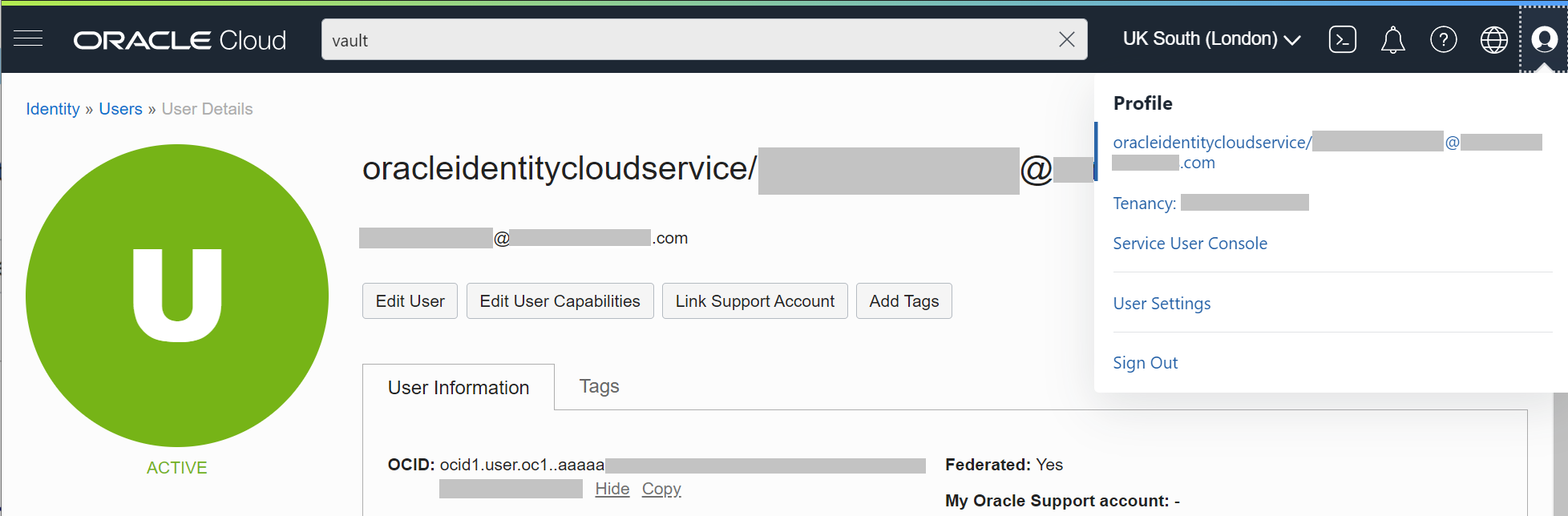
Select tenancy in the top right to see your user OCID as shown below.

Select your user in the top right to see your user OCID as shown below.
Service account key authentication
Create a secret containing your private key and fingerprint:
apiVersion: v1
kind: Secret
metadata:
name: oracle-secret
labels:
type: oracle
type: Opaque
stringData:
privateKey:
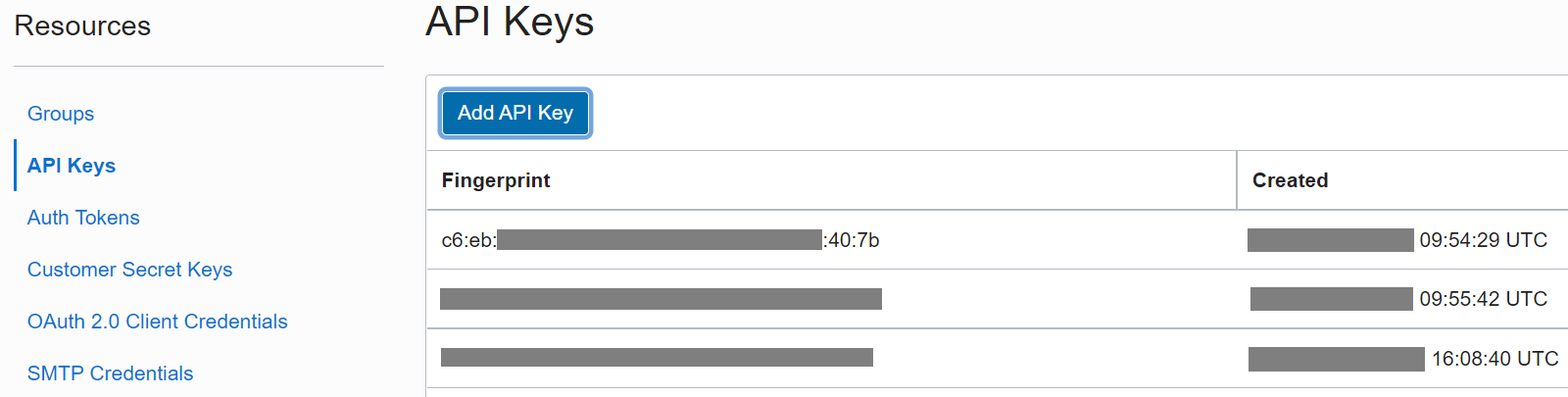
fingerprint:
Your fingerprint will be attatched to your API key, once it has been generated. Found on the same page as the user OCID.
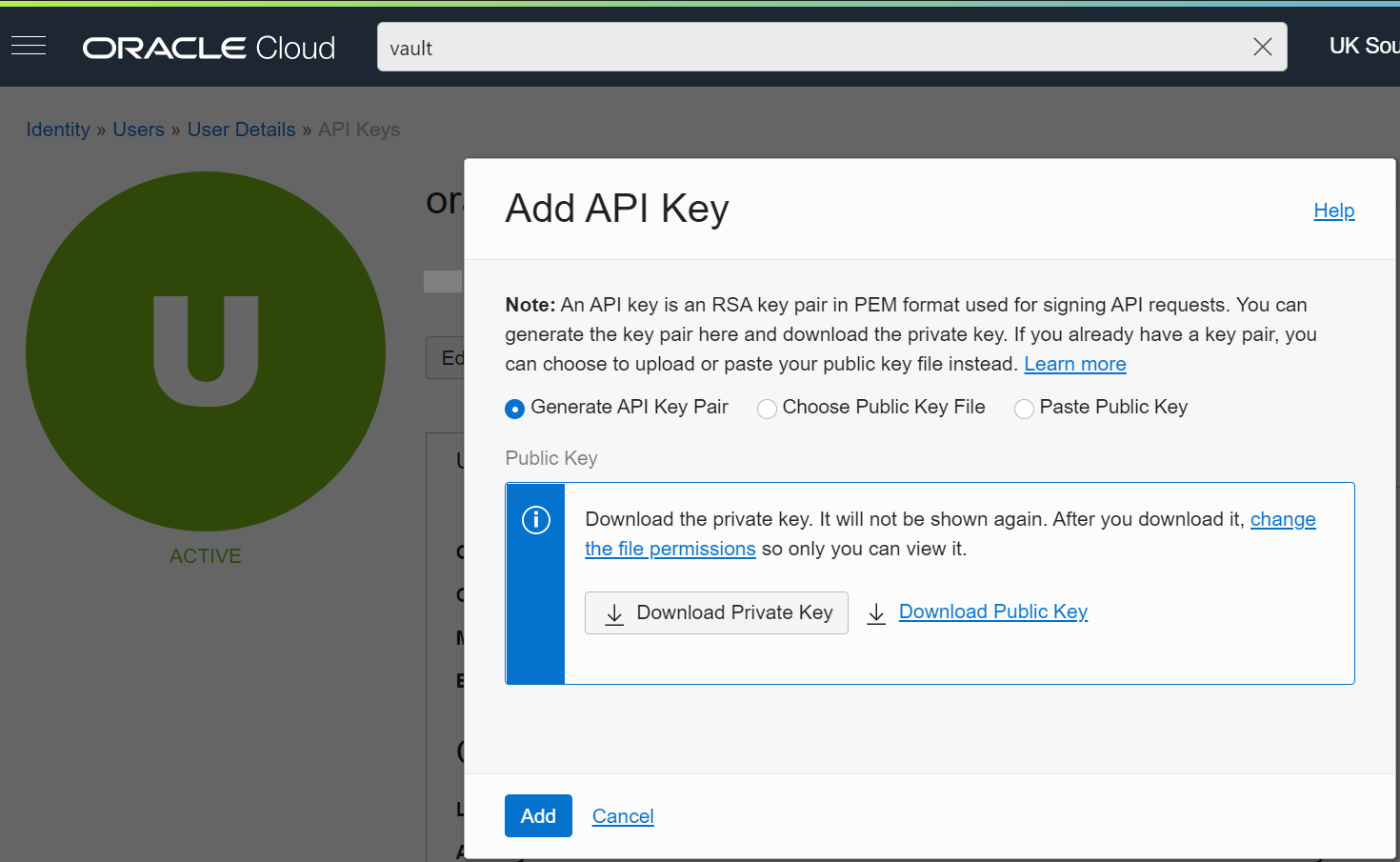
Once you click "Add API Key" you will be shown the following, where you can download the RSA key in the necessary PEM format for API requests.
This will automatically generate a fingerprint.
Update secret store
Be sure the oracle provider is listed in the Kind=SecretStore.
apiVersion: external-secrets.io/v1alpha1
kind: SecretStore
metadata:
name: example-instance-principal
spec:
provider:
oracle:
vault: # The vault OCID
region: # The vault region
---
apiVersion: external-secrets.io/v1alpha1
kind: SecretStore
metadata:
name: example-auth
spec:
provider:
oracle:
vault: # The vault OCID
region: # The vault region
auth:
user: # A user OCID
tenancy: # A user's tenancy
secretRef:
privatekey:
name: oracle-secret
key: privateKey
fingerprint:
name: oracle-secret
key: fingerprint
NOTE: In case of a ClusterSecretStore, Be sure to provide namespace in privatekey and fingerprint with the namespaces where the secrets reside.
Creating external secret
To create a kubernetes secret from the Oracle Cloud Interface secret aKind=ExternalSecret is needed.
apiVersion: external-secrets.io/v1alpha1
kind: ExternalSecret
metadata:
name: example
spec:
refreshInterval: 0.03m
secretStoreRef:
kind: SecretStore
name: example # Must match SecretStore on the cluster
target:
name: secret-to-be-created # Name for the secret on the cluster
creationPolicy: Owner
dataFrom:
- key: the-secret-name
Getting the Kubernetes secret
The operator will fetch the project variable and inject it as a Kind=Secret.
kubectl get secret oracle-secret-to-create -o jsonpath='{.data.dev-secret-test}' | base64 -d